
Augmentez votre capacité de remédiation
Corrigez aussi vite que possible les opérations illégitimes, dangereuses, les erreurs humaines, grâce à une remédiation automatisée et grâce à vos collaborateurs.
ENJEU
Réduire le temps de remédiation
Réponse à incident
Réduisez le temps de correction d’une menace
Stoppez immédiatement une compromission : un accès frauduleux, une tentative de force brute ou d’exfiltration de données.
Plans de remédiation
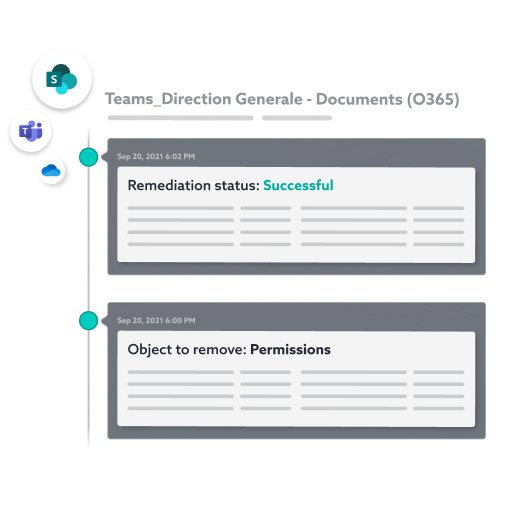
Exécutez rapidement les opérations de remédiation
Supprimez et nettoyez les droits et les permissions compromis. Pilotez d’un clic des campagnes de re-certification et de remédiation.
Maitrise dans le temps
Mettre en place une routine de supervision et de correction des données
Donnez les moyens à vos collaborateurs de gouverner et de mettre à jour les accès, les droits, les partages sur leurs données. Vous supervisez.

Difficultés
Résoudre les problématiques de sécurité et de remédiation
POURQUOI IDECSI ?
Augmentez votre capacité de réponse sur les risques
Remédiation par les utilisateurs
Vos utilisateurs gèrent leurs données jusqu’à la mise à jour des droits. Ils peuvent regrouper ou supprimer des sites ou des listes de membres, gérer les liens de partage, etc.
Automatisez les processus de remédiation
Gardez le contrôle sur les accès, les droits, les partages et les configurations de vos données.
Réduisez le coût des campagnes de re-certification en automatisant l’ensemble du processus.
Concentrez vous sur les actions essentielles.
ACTIONS COLLABORATIVES POUR UNE SECURITE RENFORCEE
La remédiation automatisée par les utilisateurs
La remédiation d’IDECSI tire parti de la connexion avec les utilisateurs et de l’alerting pour gérer automatiquement les accès, les droits, les partages et résoudre les évènements de sécurité.
Vue centralisée
Machine learning
Suivi et reporting
Implication des utilisateurs
Audit
- Audit précis des permissions sur les données, des risques ou erreurs de configuration (groupes et membres, permissions individuelles, via company link, utilisateurs internes, comptes invités ou anonymes)
- Audit des permissions sur les données sensibles
- Identification dynamique des propriétaires et possible affectation en masse
Action des utilisateurs
- Regrouper ou supprimer des sites et des listes
- Gérer les liens de partage (type companylink, externe)
- Gérer et supprimer des groupes
- Changer les propriétaires
Pilotage
- Traitement automatique des mises à jour de droits par la plateforme IDECSI
- Centralisation et consolidation des retours
- Outil de supervision pour les équipes SSI et SOC
Maîtrise dans le temps
- Changements et mises à jour réalisés en continu
- Alerting en cas de changement majeur

Autres solutions
Des réponses performantes à chacun de vos défis
Gouvernance Microsoft 365 :
Discutons de votre projet ?


